Experts agree we need new key-exchange and signature algorithms—so we can resist attacks from quantum computing. Several organizations have had a go at selecting some, but now the National Institute of Standards and Technology has weighed in.
That’s significant because NIST is the same body that standardized AES and SHA-3. We can’t wait until quantum computing is capable of breaking today’s encryption, because would-be attackers are already archiving data in transit. Devs are advised to ensure they have “crypto agility”—the ability to swap in new algorithms with ease.
NIST and others want us to get ahead of the curve. In this week’s Secure Software Blogwatch, we try to forget BULLRUN.
Your humble blogwatcher curated these bloggy bits for your entertainment. Not to mention: PMD.
[ Get key takeaways from a survey of 300+ professionals on software security. Or, download the full report: Flying Blind: Firms Struggle to Detect Software Supply Chain Attacks ]
NIST’s nice PQC picks
What’s the craic? Lucas Ropek reports—“The Government's Fight Against Quantum Hackers”:
“A matter of national security”
For the most part, today’s popular encryption standards are very strong and difficult to defeat. … But researchers worry about a future in which quantum computing … will be able to swiftly unscramble those digital defenses without breaking a sweat. … That’s where the new encryption standards will come in handy.
…
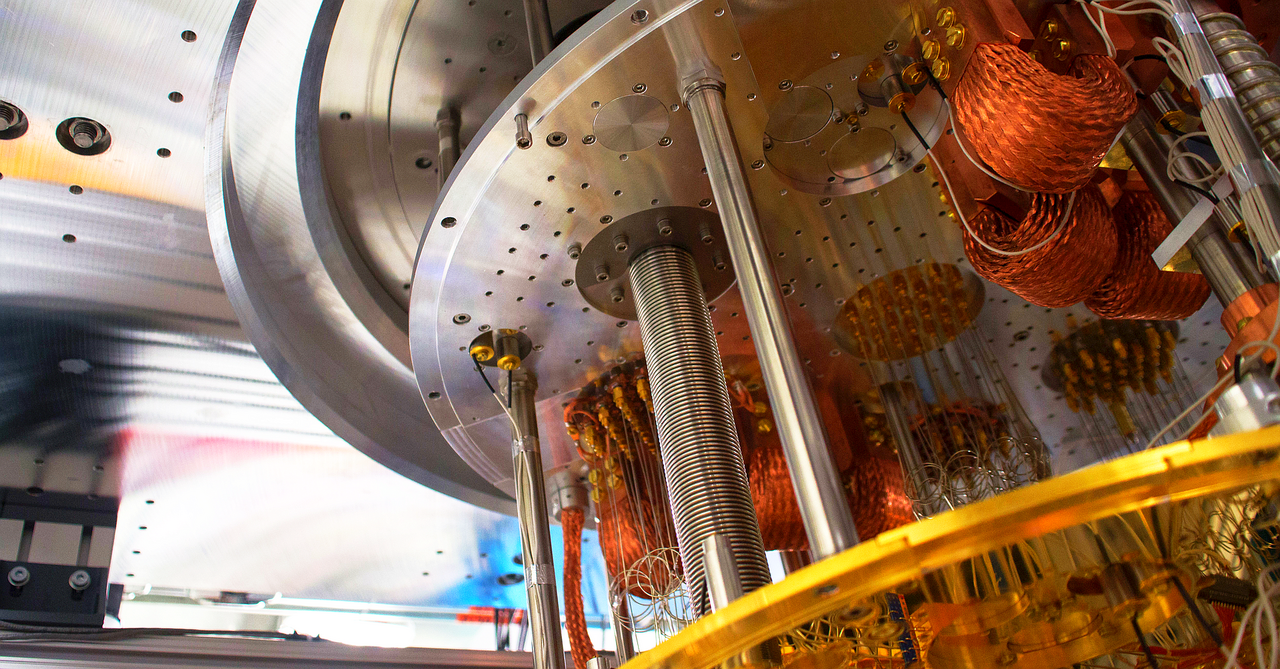
Quantum computing … differs from “classical” computing in that it is designed to operate using the properties of quantum mechanics. … Theoretically, the processing power of quantum computers could be [far] greater than the devices that exist today. … As a new development in the realm of internet security, NIST’s … new “quantum-resistant” encryption … algorithms are a pretty big deal.
…
NIST has consistently been at the forefront of creating the digital protections that we all rely upon daily. The most widely used encryption cipher, … AES, was generated via a previously held NIST competition. So was the third iteration of … SHA, the critical cryptographic function that is used ubiquitously. … The concerns about quantum decryption aren’t just about keeping the average American’s text messages safe; they’re also a matter of national security.
So what are we getting? Marilyn Cohodas fills in the blanks—“NIST Picks 4 Quantum-Resistant Cryptographic Algorithms”:
“Threats could be reality as soon as 2030”
The chosen algorithms are CRYSTALS-Kyber for general encryption to access secure websites and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures. [It] will help enterprises prepare their environments for the time when quantum computers will be powerful — and … available — enough that they will be able to break present-day encryption.
…
Attackers are … harvesting and hoarding sensitive information with the expectation that they can crack it later when quantum computing methods become available. … Any digital system that uses public standards for public-key cryptography could be vulnerable to an attack by quantum computers in the future. … Researchers estimate that [these] threats could be reality as soon as 2030.
Wait, what? 2030? Why worry today? Amit Katwala clarifies—“Quantum-proof encryption is here—decades before it can be put to the test”:
“Data may be vulnerable now”
Those quantum threats might still be decades away, but security experts warn of “harvest now, decrypt later” attacks—bad actors hoovering up caches of encrypted data with the expectation that they’ll eventually have a quantum computer that can access them. The longer it takes to implement quantum-proof cryptography, the more data will be vulnerable.
…
Over the next two years, NIST will publish draft standards, invite comments, and finalize the new forms of quantum-proof encryption, which it hopes will be adopted across the world. After that … it could be 10 to 15 years before companies implement them widely, but their data may be vulnerable now.
Okay but is it eight years or “decades”? Here’s hannob:
I've been following this space for a while and this is a good question. … I think the answer is really a "range from 10 years to never."
…
There's a lot of investment currently in the quantum computer space (plus a lot of hype and scams). Yet this is still all very early research and far away from any practical use. The challenges to really build a QC that can break cryptography are enormous — and it is absolutely a possibility that they're too big to overcome.
How did we get here? Bas Westerbaan tells us, “How we got here”:
“This is a big moment for the Internet”
Our story starts in 1994, when mathematician Peter Shor discovered a marvelous algorithm that efficiently factors numbers and computes discrete logarithms. With it, you can break nearly all public-key cryptography deployed today. [But] Shor’s algorithm … needs a quantum computer. Back in 1994, quantum computers existed only on paper.
…
Shor’s algorithm breaks all widely deployed key agreement and digital signature schemes, which are both critical to the security of the Internet … (symmetric encryption [is] as far as known, secure against quantum attacks). … NIST, known for standardizing AES and SHA, opened a public competition to select which post-quantum algorithms they will standardize. Cryptographers from all over the world submitted algorithms and publicly scrutinized each other’s. … From the original 82 submissions, eight made it into the final third round. From those eight, NIST chose one key agreement scheme … Kyber, which is a Key Encapsulation Mechanism (KEM) … and three signature schemes.
…
So can we switch to post-quantum TLS today? … We have to be a bit careful: Some TLS implementations are brittle and crash on the larger KeyShare message that contains the bigger post-quantum keys. … In the coming months, many languages, libraries and protocols will already add preliminary support. … A different aspect … is crypto agility: Being able to switch to a new algorithm/implementation in case of a break. Let’s hope that we will not need it, but now we’re going to switch, it’s nice to make it easier in the future. … This is a big moment for the Internet.
Size is important. Or so jd says:
The signature lengths in these schemes [are] impressive. Falcon was recently congratulated for bringing the hash down to 410 bytes (not bits!). … If you thought getting SHA-2 and SHA-3 into Git was bad, Falcon is going to be an absolute nightmare.
…
This really is an improvement on the others. Dilithium reports a signature size of 2420 bytes and I believe SPHINCS+ produces one that is even longer.
You, too, can play with them, not only through the reference implementations but also through BouncyCastle, which has implementations of these algorithms. I wouldn't be surprised if they were being added to other standard crypto libraries, so expect some usage of them in the near future.
A reminder that NIST is part of the U.S. Department of Commerce. But has NoneSuch confused it with “No Such Agency”?
So the NSA, the largest employer of mathematicians in the world and well known for building flaws into all past encryption methods, tells you to use these four algorithms and you think anything encrypted with them is safe.
But why should we trust NIST? Isn’t this the same org that standardized the Dual_EC_DRBG “backdoor”? tptacek gets it:
We get it. People don't like NIST, because of BULLRUN. [But] NIST competitions are legitimated by their participants. People trust NIST's hash competition because of who entered, and because the winning team has an unimpeachable record. For the most part, people will trust this contest for similar reasons.
…
Pull up the authorship team on CRYSTALS-KYBER. Approximately 0% of credible cryptographers believe that NIST was somehow able to exert improper influence over this design.
Meanwhile, The Oncoming Scorn is simultaneously serious and snarky, probably:
Actual quantum computers don't exist yet. … Or do they?
And Finally:
You have been reading Secure Software Blogwatch by Richi Jennings. Richi curates the best bloggy bits, finest forums, and weirdest websites … so you don’t have to. Hate mail may be directed to @RiCHi or ssbw@richi.uk. Ask your doctor before reading. Your mileage may vary. E&OE. 30.



