March 20, 2023
Experts weigh in on a new OpenSSF SLSA framework survey — and the overall state of supply chain security practices.
March 15, 2023
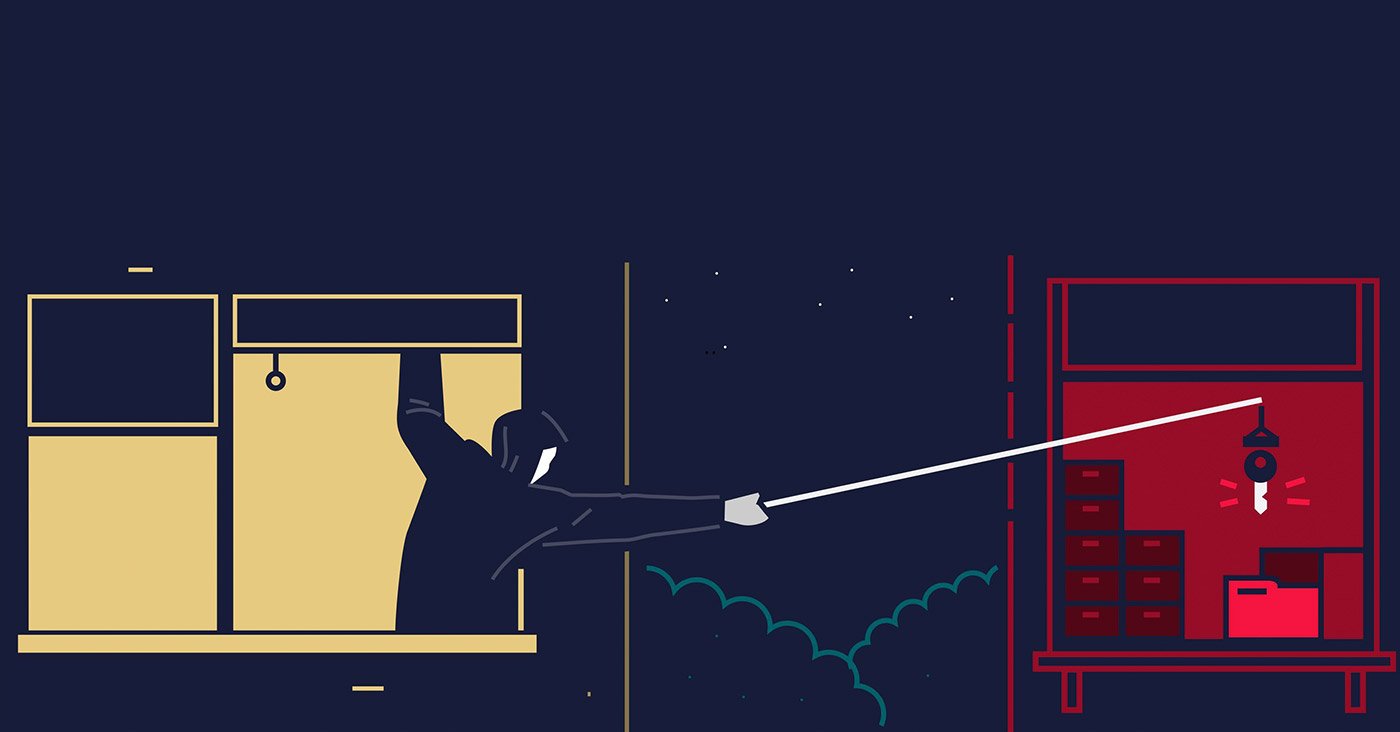
GitHub is a weak link in the software supply chain. Finally, Microsoft is doing something about it — by forcing users into two-factor authentication (2FA).
March 14, 2023
Here’s how attackers are finding software development secrets buried in code repositories — and exploiting them.
March 9, 2023
Here are the key takeaways from the Colour-Blind remote access trojan, with insights from supply chain security experts.
March 7, 2023
The new National Cybersecurity Strategy will punish big software developers for failing to follow best practices. And, for the first time, make them liable.
March 7, 2023
Here's what you need to know about app sec's addiction to vulnerabilities — and why application security needs to evolve to take on supply chain security.